Spoof Mac Address Os X Software
- Best Mac Os X Software
- Spoof Mac Address On Mac
- Spoof Mac Address Os X Software 2017
- Mac Os X Free Software
MAC spoofing is a technique for changing a factory-assigned Media Access Control (MAC) address of a network interface on a networked device. The MAC address that is hard-coded on a network interface controller (NIC) cannot be changed. However, many drivers allow the MAC address to be changed. Additionally, there are tools which can make an operating system believe that the NIC has the MAC address of a user's choosing. The process of masking a MAC address is known as MAC spoofing. Essentially, MAC spoofing entails changing a computer's identity, for any reason, and it is relatively easy.[1]
Motivation[edit]
The changing of the assigned MAC address may allow the bypassing of access control lists on servers or routers, either hiding a computer on a network or allowing it to impersonate another network device. MAC spoofing is done for legitimate and illicit purposes alike.
MAC spoofing is a technique for changing a factory-assigned Media Access Control (MAC) address of a network interface on a networked device. The MAC address that is hard-coded on a network interface controller (NIC) cannot be changed. However, many drivers allow the MAC address to be changed.
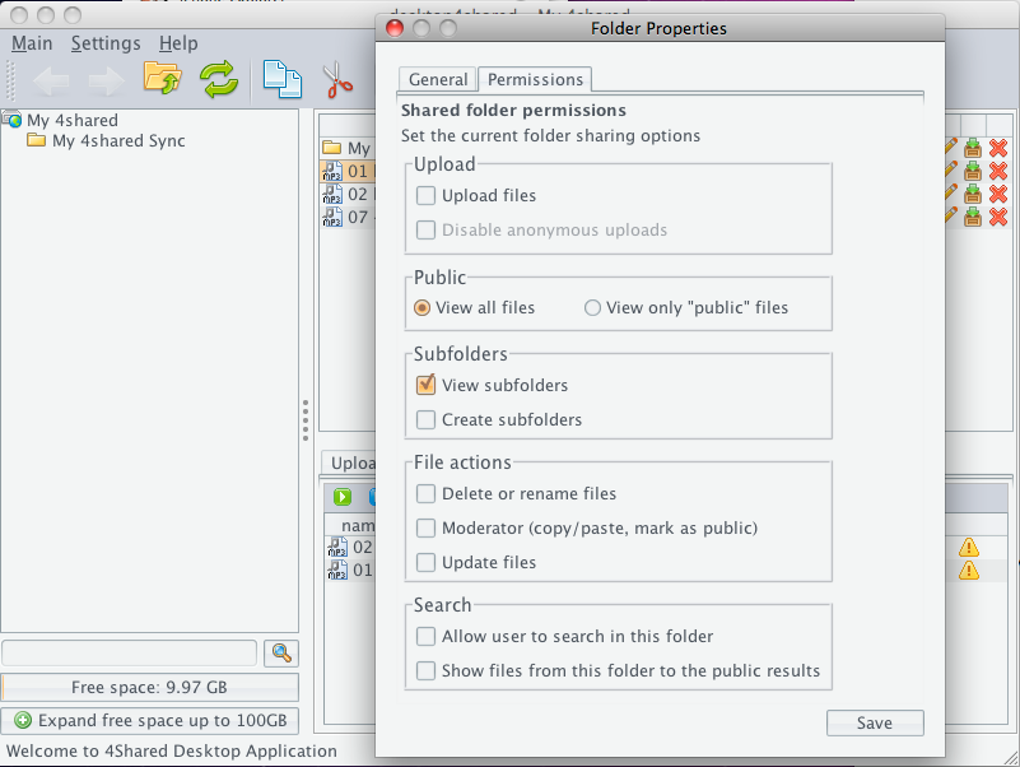
MacSpoofer is a FREE mac address spoofer for Mac OS X. After installing MacSpoofer you will be able to change your MAC address from the system preferences. Jul 23, 2016 Today we will focus on how you can change your MAC Address on your OS X device. Before we do that, lets ask ourselves a couple of simple questions, why would we want to ‘Spoof’ our own MAC Address? Is it safe to fake your MAC Address? Lets find out. Spoof Your MAC ADDRESS On A Mac. Retrieving your current MAC address. To mask a MAC address, you just need to access the network settings on the Windows control panel and define a new identification number in the software. The operating system will now send data packets with the user-defined MAC address in the local network. The following step-by-step tutorial explains MAC spoofing using Windows 7. Jul 03, 2016 Mac Spoofing on Microsoft Windows, OS X and Linux July 3, 2016 by Nathan House In this video we explore mac spoofing, why you might want to spoof your mac address and how to actually change your mac on all platforms Microsoft Windows, Mac OS X and Linux.
New hardware for existing Internet Service Providers (ISP)[edit]
Many ISPs register the client's MAC address for service and billing services.[2] Since MAC addresses are unique and hard-coded on network interface controller (NIC) cards,[1] when the client wants to connect a new gadget or change their existing gadget, the ISP will detect different MAC addresses and the ISP might not grant Internet access to those new devices. This can be circumvented easily by MAC spoofing. The client only needs to spoof the new device's MAC address to the MAC address that was registered by the ISP.[2] In this case, the client spoofs their MAC address to gain Internet access from multiple devices. While this seems like a legitimate case, MAC spoofing new gadgets can be considered illegal if the ISP's user-agreement prevents the user from connecting more than one device to their service. Moreover, the client is not the only person who can spoof their MAC address to gain access to the ISP. Hackers can gain unauthorized access to the ISP via the same technique. This allows hackers to gain access to unauthorized services, and the hacker will be hard to identify because the hacker uses the client's identity. This action is considered an illegitimate use of MAC spoofing and illegal as well. However, it is very hard to track hackers that are utilizing MAC spoofing.[3]
This also applies to customer-premises equipment, such as cable and DSL modems. In cases where the provider leases the equipment to the customer on a monthly basis, the CPE has a hard-coded MAC address which is on a list known to the provider's distribution networks, allowing service to be established as long as the customer is not in billing arrears. In cases where the provider allows customers to provide their own equipment (and thus avoid the monthly leasing fee on their bill,) the provider requires that the customer give them the MAC address of their equipment before service will be established.
Fulfilling software requirements[edit]
Some software can only be installed and run on systems with pre-defined MAC addresses as stated in the software end-user license agreement, and users have to comply with this requirement in order to gain access to the software. If the user has to install different hardware due to malfunction of the original device or if there is a problem with the user's NIC card, then the software will not recognize the new hardware. However, this problem can be solved using MAC spoofing. The user just has to spoof the new MAC address as to mimic the MAC address that was registered by the software.[citation needed] This activity is very hard to define as either legitimate or illegitimate reason for MAC spoofing. Legal issues might arise if the user grants access to the software on multiple devices simultaneously. At the same time, the user can obtain access to software for which he or she has not secured a license. Contacting the software vendor might be the safest route to take if there is a hardware problem preventing access to the software. Software may also perform MAC filtering because the software does not want unauthorized users to gain access to certain networks to which the software grants access. In such cases MAC spoofing can be considered a serious illegal activity and can be legally punished.[4]
Identity masking[edit]
If a user chooses to spoof their MAC address in order to protect the user's privacy,[citation needed] this is called identity masking. One might wish to do this because, as an example, on a Wi-Fi network connection a MAC address is not encrypted. Even the secure IEEE 802.11i-2004 (WPA) encryption method does not prevent Wi-Fi networks from sending out MAC addresses.[citation needed] Hence, in order to avoid being tracked, the user might choose to spoof the device's MAC address. However, hackers use the same technique to maneuver around network permissions without revealing their identity. Some networks use MAC filtering in order to prevent unwanted access. Hackers can use MAC spoofing to get access to a particular network and do some damage. Hackers' MAC spoofing pushes the responsibility for any illegal activity onto authentic users. As a result, the real offender may go undetected by law enforcement.[citation needed]
MAC Address Randomization in WiFi[edit]
Best Mac Os X Software
To prevent third parties from using the MAC address to track devices, Android, Linux, iOS, and Windows[5] have implemented MAC addressrandomization. In June 2014, Apple announced that future versions of their iOS platform would randomize MAC addresses for all WiFi connections. The Linux kernel has supported MAC address randomization during network scans since March 2015,[6] but drivers need to be updated to use this feature.[7] Windows has supported it since the release of Windows 10[5] in July 2015.
Controversy[edit]
Although MAC address spoofing is not illegal, its practice has caused controversy in some cases. In the 2012 indictment against Aaron Swartz Internet hacktivist, who was accused of illegally accessing files from JSTOR digital library, prosecutors claimed that because he had spoofed his MAC address it showed purposeful intent to commit criminal acts.[4] In June 2014, Apple announced that future versions of their iOS platform would randomize MAC addresses for all WiFi connections, making it more difficult for internet service providers to track user activities and identities, which resurrected moral and legal arguments surrounding the practice of MAC spoofing among several blogs and newspapers.[8]
Limitations[edit]
MAC address spoofing is limited to the local broadcast domain. Unlike IP address spoofing, where senders spoof their IP address in order to cause the receiver to send the response elsewhere, in MAC address spoofing the response is usually received by the spoofing party if switch is not configured to prevent MAC spoofing.
See also[edit]
- ifconfig, linux utility capable of changing MAC address
References[edit]
- ^ abCardenas, Edgar D. 'MAC Spoofing--An Introduction'. GIAC Security Essentials Certification. SANS Institute. Retrieved 8 February 2013.
- ^ ab'MAC Spoofing'. Royal Canadian Mounted Police. Research and Development Section in Collaboration with the NCECC’s Technology Unit. Archived from the original on 23 June 2012. Retrieved 8 February 2013.
- ^Gupta, Deepak; Gaurav Tiwari (4 November 2009). 'MAC SPOOFING AND ITS COUNTERMEASURES'(PDF). International Journal of Recent Trends in Engineering. 2 (4): 21. Retrieved 8 February 2013.
- ^ abIndictment against Aaron Swartz
- ^ abhttp://papers.mathyvanhoef.com/asiaccs2016.pdf
- ^https://w1.fi/cgit/hostap/plain/wpa_supplicant/ChangeLog
- ^https://git.kernel.org/pub/scm/linux/kernel/git/torvalds/linux.git/commit/?id=ad2b26abc157460ca6fac1a53a2bfeade283adfa
- ^Change MAC Address: Use Public WiFi Signals Without Any Limits, Not To Mention Serious Privacy Benefits
MAC or “Media Access Control” Address is hardware address assigned to network interface devices. So, your laptop, smartphone, WiFi radio, each of them have a separate and fixed MAC address. While connecting your device to a network (e.g., WiFi Hotspot), your MAC address is recorded there. The owner can’t directly identify if it’s your device but he can see it’s MAC address and block it if he finds it annoying.
https://wonderrenew442.weebly.com/blog/avc-intra-codec-download-mac. Normal users can’t directly change it on their will so it works fine. But if you know how to “spoof” or “change” your device’s MAC address then even after blocking your MAC address, you can still connect your device to your desired network by changing your mac address. Not only this, you can enjoy few more benefits as mentioned below –
- You can stay anonymous in a network
- Some networks or (confidential) websites allow only specific range of MAC address devices to connect to them. So, if you know the list or range, you can change your device’s MAC address accordingly to connect to the server.
- You can be tracked using your MAC address. Many technologies tracked users using their MAC address which they received when user tried to connect the device to a public network or WiFi. Concerning this fact, Apple developers have put random MAC address concept to their iOS 8 operating system to prevent users from being tracked without their consent.
- Some public networks which allow Free WiFi put the limitation on each device (actually on their MAC address) to use their network for like 30 minutes. After that, the MAC address automatically gets blocked. So, if you know spoofing of MAC address, you can enjoy free WiFi for an unlimited time by changing MAC address when it’s blocked.
And, Yes! It’s legal. MAC address assigned in a factory and it’s legal to change your device’s MAC address.
View installed software on mac. So here in this article, we are going to show how to change or spoof MAC address in your Windows Operating System. Although, we are providing this guide through our Windows 10 OS but steps are similar for Windows 8.1, 8 and 7 OS. Scroll down to know how to change MAC address in Windows 10.
List All Network Adapters with their MAC Address
Before changing MAC address of your PC, you first need to check if there are more than one network interface hardware in your device as each of them have different MAC address and you need to change only that using which you connects to a network.
So, open command prompt either by typing “command prompt” or “cmd” at Cortana bar or Windows search bar or by opening RUN dialog box by pressing Win+R and typing “cmd” in there and hit ENTER! Best blu ray software for mac pro.
Now in the command prompt window type –
cd
getmac /v /fo list
Hit ENTER !
It will show all network interface devices available in your device with their Physical Address (MAC Address) :-
Now, you know which network adapter’s MAC Address you intend to change. Lets assume you want to change your WiFi adapter’s MAC Address. As shown on screenshot above, my WiFi network adapter’s name is “Qualcomm Atheros AR956x Wireless Network Adapter”.
So, to change the network adapter’s MAC Address, follow the instructions provided below.
Steps to Spoof MAC Address in Windows 10 PC or Laptop
Step 1:- Right Click on the Start (Windows icon on the bottom left). From the context menu, choose ‘Network Connections’.
Spoof Mac Address On Mac
Step 2:- On the opened window screen, locate your desired network adapter, right-click on it and go to its properties.
Step 3:- At this WiFi Properties screen, click “Configure” to open your network adapter’s property screen.
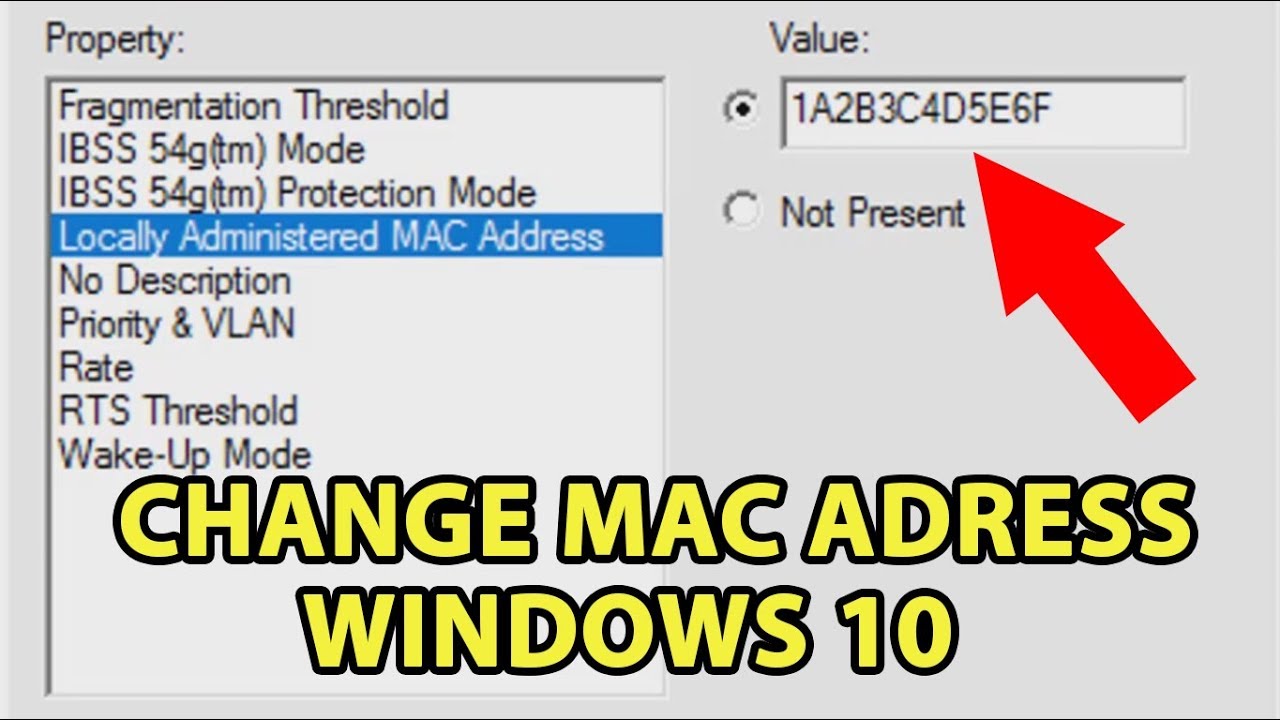
Step 4:- Go to “Advanced” Tab. From the list of available options, select “Network address” or Local Administered MAC Address, whichever is available.
Step 5:- Upon selection, you will see a text box saying ‘Value’. This is the place where you need to enter your custom MAC address. Enter six digit alphanumeric code here (without any dashes or colon). For example – enter 0A54EG70HH11 in the value text box if you want so set the network adapter’s MAC Address 0A:54:EG:70:HH:11
Spoof Mac Address Os X Software 2017
Step 6 :- Click OK and close other opened window or dialog box.
And, it’s done!
Mac Os X Free Software
To verify if you have successfully spoofed your MAC address, you can run command prompt commands mentioned above to check if your network adapter’s MAC address spoofed or not.